今日Github官方发布安全公告称:修复了git客户端里的一个高危安全漏洞(CVE-2014-9390) 影响包括windows及Mac等系统下的所有git客户端
详见:https://github.com/blog/1938-git-client-vulnerability-announced
The vulnerability concerns Git and Git-compatible clients that access Git repositories in a case-insensitive or case-normalizing filesystem. An attacker can craft a malicious Git tree that will cause Git to overwrite its own .git/config file when cloning or checking out a repository, leading to arbitrary command execution in the client machine. Git clients running on OS X (HFS+) or any version of Microsoft Windows (NTFS, FAT) are exploitable through this vulnerability. Linux clients are not affected if they run in a case-sensitive filesystem.
测试方法:git clone http://gitcasefail.googlecode.com/svn/trunk/repo/ 弹计算器说明漏洞存在

//@heige
Mac升级方法:brew install git 然后
cd /usr/bin
sudo mkdir old-git
sudo mv git* old-git
然后运行git –version查看版本 升级ok
http://article.gmane.org/gmane.linux.kernel/1853266
This is a security-fix for CVE-2014-9390, which affects users on Windows and Mac OS X but not typical UNIX users.
A set of new releases for older maintenance tracks (v1.8.5.6, v1.9.5, v2.0.5, and v2.1.4) are published at the same time and they contain the same fix.
Various implementations and ports, including Git for Windows, Git OSX installer, JGit & EGit, libgit2 (and Visual Studio which uses it)have been updated at the same time.Even though the issue may not affect Linux users, if you are a hosting service whose users may fetch from your service to Windows or Mac OS X machines, you are strongly encouraged to update to protect such users who use existing versions of Git.
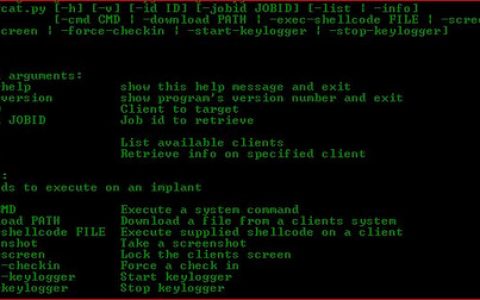
玄机在这里:http://gitcasefail.googlecode.com/svn/trunk/.Git/hooks/post-checkout
calc.exe calc open /Applications/Calculator.app/ gnome-calculator
* We used to allow committing a path “.Git/config” with Git that is
running on a case sensitive filesystem, but an attempt to check out
such a path with Git that runs on a case insensitive filesystem
would have clobbered “.git/config“, which is definitely not what
the user would have expected. Git now prevents you from tracking
a path with “.Git” (in any case combination) as a path component.* On Windows, certain path components that are different from “.git”
are mapped to “.git”, e.g. “git~1/config” is treated as if it were
“.git/config”. HFS+ has a similar issue, where certain unicode
codepoints are ignored, e.g. “.g\u200cit/config” is treated as if
it were “.git/config“. Pathnames with these potential issues are
rejected on the affected systems. Git on systems that are not
affected by this issue (e.g. Linux) can also be configured to
reject them to ensure cross platform interoperability of the hosted
projects.* “git fsck” notices a tree object that records such a path that can
be confused with “.git”, and with receive.fsckObjects configuration
set to true, an attempt to “git push” such a tree object will be
rejected. Such a path may not be a problem on some filesystems
but in order to protect those on HFS+ and on case insensitive
filesystems, this check is enabled on all platforms.
参考来源:Scanv & gmane
原创文章,作者:老D,如若转载,请注明出处:https://laod.cn/318.html